|
Create SSC for Hyper-V Replica - Step by step with screenshots
To enable Windows 2012 Hyper-V Replica in a workgroup environment, we
recommend to choose Certificate-base Authentication (HTTPS). Otherwise, you
may have a problem to configure it. Please refer to this page:
Should I use Kerberos authentication (HTTP)
or Certificate-base Authentication (HTTPS) in Hyper-v Replica - Step by step with screenshots .
This article will show you how to create Self-Signed Certificate in Windows
2012Hyper-V replica.
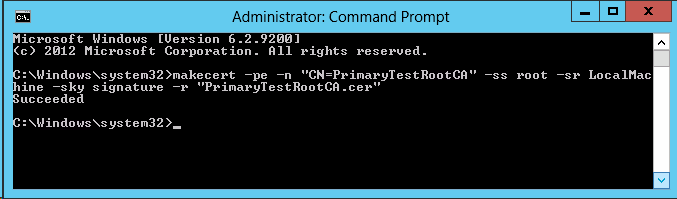
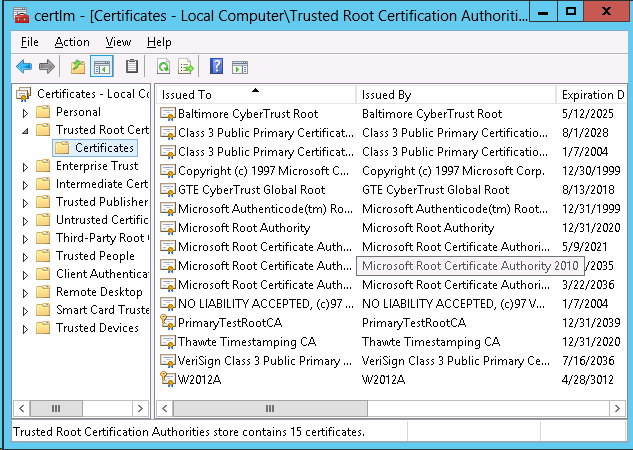
A. On the Primary Server, Win2012A in our case, create PrimaryTestRootCA.
1. Download the makecert.exe utility from the Microsoft website.
2. Run the following elevated command to create a self-signed root authority
certificate to installs a certificate in the root store of the local
machine and is saved as a file locally:
makecert -pe -n "CN=PrimaryTestRootCA" -ss root -sr LocalMachine -sky
signature -r "PrimaryTestRootCA.cer"
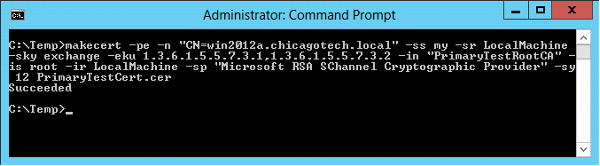
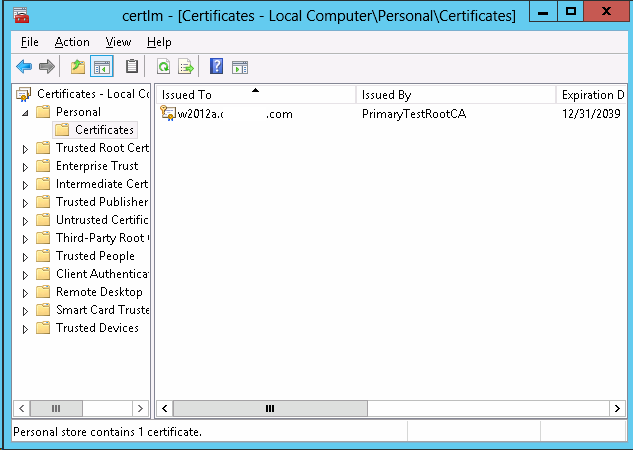
3. Run the following elevated command to installs a certificate in the
Personal store of the local machine and is saved as a file locally:
makecert -pe -n "CN=<FQDN>" -ss my -sr LocalMachine -sky exchange -eku
1.3.6.1.5.5.7.3.1,1.3.6.1.5.5.7.3.2 -in "PrimaryTestRootCA" -is root -ir
LocalMachine -sp "Microsoft RSA SChannel Cryptographic Provider" -sy 12
PrimaryTestCert.cer
Where <FQDN> is the Primary Server FQDN
B.
On the Replica Server, Win2013B, create RecoveryTestRootCA.
1. Copy the makecert.exe the the Replica server.
2. Run the following elevated command to Create a self-signed root authority
certificate
makecert -pe -n "CN=RecoveryTestRootCA" -ss root -sr LocalMachine -sky
signature -r "RecoveryTestRootCA.cer"
3. Run the following elevated command to create a new certificate signed by
the test root authority certificate
makecert -pe -n "CN=<FQDN>" -ss my -sr LocalMachine -sky exchange -eku
1.3.6.1.5.5.7.3.1,1.3.6.1.5.5.7.3.2 -in "RecoveryTestRootCA" -is root -ir
LocalMachine -sp "Microsoft RSA SChannel Cryptographic Provider" -sy 12
RecoveryTestCert.cer
Where <FQDN> is the Replica Server FQDN
The command installs a test certificate in the Personal store of the local
machine and is saved as a file locally. The certificate can be used for both
Client and Server authentication.
C.
Finishing Up
1. Follow this
How to export a Certificate in Windows - Step by step with screenshots
to export certificate on primary server/Recovery server and copy it to
Recovery server/Primary Server.
2. In the primary server run:
certutil -addstore -f Root "PrimaryTestRootCA.cer"
3. In Primary server, run:
certutil -addstore -f Root "RecoveryTestRootCA.cer"
4. By default, a certificate revocation check is mandatory and Self-Signed
Certificates don’t support Revocation checks. Hence, both modify the
following registry key on both the Primary and Replica servers to disable
the CRL check
reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Virtualization\Replication"
/v DisableCertRevocationCheck /d 1 /t REG_DWORD /f
The above step (3) is applicable if the CRL is inaccessible in general.
Post your questions, comments, feedbacks and suggestions
Contact a consultant
Related Topics
|

This web is provided "AS IS" with no warranties.